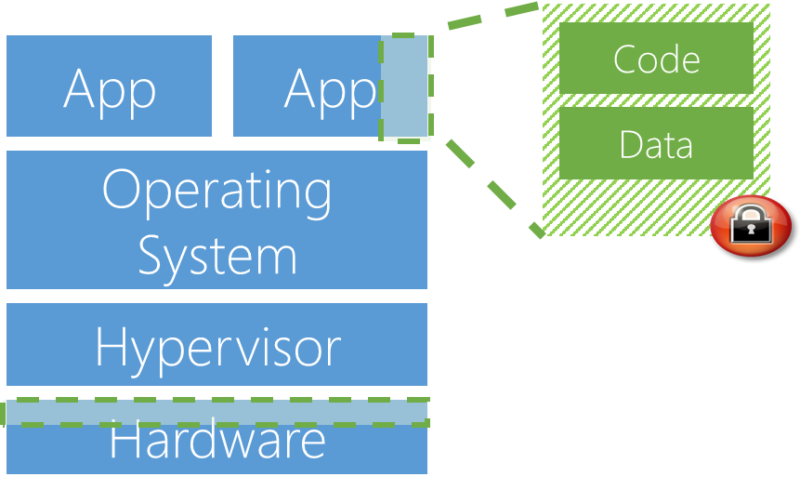
Enlarge / The Trusted Execution Environment means that, even if the application and operating system are compromised, the green code and data can't be accessed. (credit: Microsoft)
Microsoft announced today a new feature coming to its Azure cloud platform named "Confidential Compute." The feature will allow applications running on Azure to keep data encrypted not only when it's at rest (in storage) or in transit (over a network) but when it's being computed on in-memory. This ability to encrypt data when it's in-use means that it can be kept secure even from Microsoft's administrators, government warrants, and hackers.
Confidential Computing will have two modes: one is built on virtual machines, while the other uses the SGX ("Software Guard Extensions") feature found in Intel's recently introduced Skylake-SP Xeon processors. Both modes will allow applications to ringfence certain parts of their code and data so that they operate in a "trusted execution environment" (TEE). Code and data that are inside a TEE cannot be inspected from outside the TEE.
The virtual machine mode uses the Virtual Secure Mode (VSM) functionality of Hyper-V that was introduced in Windows 10 and Windows Server 2016. With VSM, most parts of an application will run in a regular virtual machine atop a regular operating system. The protected, TEE parts will run in a separate virtual machine containing only a basic stub operating system (enough that it can communicate with the regular VM) and only those parts of the application code that need to handle the sensitive data.