It's akin to warning someone not to brush her teeth with a brick or to dry her hair with a blow torch, but based on numerous links circulating on Twitter Thursday morning, it bears saying: don't post sensitive account credentials to GitHub, or any other code repository.
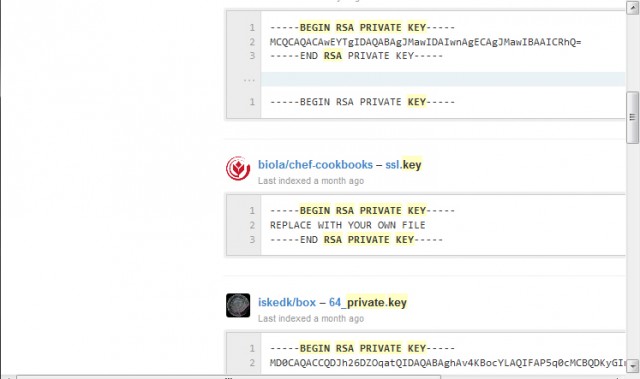
On Thursday morning, the microblogging site was awash with messages linking to passwords and private cryptographic keys that are publicly accessible. Searches like this, this, and this turned up dozens of accounts that appeared to be exposing credentials that should never be made public. (Just minutes before Ars published this post, the searches stopped working, most likely as a result of GitHub admins who were trying to save users from their own carelessness. Many of the same GitHub accounts could still be located using Google, however.) Assuming they're still being used to log in to valid accounts, their exposure compromises the entire security that users attempted to establish when they generated the keys in the first place.
Ars won't be calling out individual accounts, although one GitHub offender appeared to reveal a password for an account on Chromium.org, the repository that stores the source code for Google's open-source browser. An eagle-eyed security researcher reported finding "an ssh password to a production server of a major, MAJOR website in China." Another tweet showed what appeared to be a sensitive GitHub authentication token used by a prominent front end developer for Bitly. In the wrong hands, a valid token could help miscreants redirect millions of people to malicious sites.
Read 3 remaining paragraphs | Comments