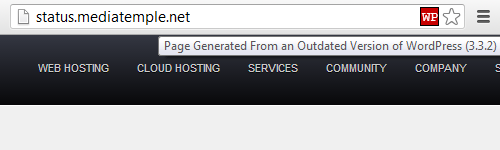
When it comes to keeping your website secure your web host should be the least of your worries. These are technology companies, sometimes rather large, whose focus is on websites. You would think that they would be better at handling website security than anyone other security professionals. Unfortunately we often find that they are not. As just one example, last year we discussed the fact that Media Temple was incorrectly blaming a hack of websites hosted by them on their customers running outdated software on their websites, while they themselves were running outdated software on their website. Over a year later they are still are not bothering to take the basic step of keeping software running on their website up to date:
Trying to access the security of web hosts is difficult because much of the information needed to do that assessment is only available to them. There are some things that you can check on and one of those is whether they are keeping the version of PHP on the server hosting your website up to date. If you are using WordPress, Joomla, Drupal, or a lot of other web software then you are using PHP and it is important to keep that up to date, as a hacked website we cleaned up this week shows.
One of the basic steps of cleaning up a hacked website is determining how it was hacked and then fixing the vulnerability so that the website doesn’t get hacked again (unfortunately, many companies that clean up hacked websites cut corners and don’t do this). In reviewing the log files for the website in question we traced the original exploitation to this line in the website’s access log:
91.224.160.25 – - [16/Apr/2013:19:18:32 -0400] “POST /?-d+allow_url_include%3d1+-d+auto_prepend_file%3dphp://input HTTP/1.1″ 200 68
What that shows is that a vulnerability in PHP versions prior to 5.3.13 and 5.4.3 was attempting to be exploited. Unfortunately the website in question was running an older vulnerable version of PHP and was configured in a way that made it susceptible to the vulnerability. If PHP had been kept up to date the website would not have been hacked.
The PHP developers fairly regularly release new versions that fix security vulnerabilities in the software. The most recent releases with security fixes were versions 5.3.23 and 5.4.13, released in March. Unfortunately, we often find that our client’s web hosts are not keeping PHP up to date. If your web host isn’t keeping PHP updated you probably should move to a web host that takes such basic security seriously.
If you are wondering what version of PHP your web host is using for your website there are a number of ways to find that out. The least technical way to do that is to contact their customer support and ask them what version of PHP in use. It would also be good to ask them what their upgrade policy is for PHP and other software powering the web server, to make sure that they properly handling that. You can sometimes find the PHP version in use in the control panel for your website or the administrative area of the website. You can also use a tool we have created that allows you to check the version of various software running the server your website is on.