Computer scientists say they found a way to sneak malicious programs into Apple's exclusive app store without being detected by the mandatory review process that's supposed to automatically flag such apps.
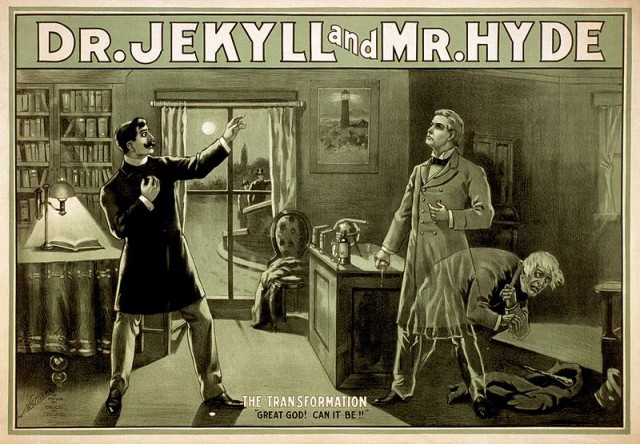
The researchers from the Georgia Institute of Technology used the technique to create what appeared to be a harmless app that Apple reviewers accepted into the iOS app store. They were later able to update the app to carry out a variety of malicious actions without triggering any security alarms. The app, which the researchers titled "Jekyll," worked by taking the binary code that had already been digitally signed by Apple and rearranging it in a way that gave it new and malicious behaviors.
"Our method allows attackers to reliably hide malicious behavior that would otherwise get their app rejected by the Apple review process," the researchers wrote in a paper titled Jekyll on iOS: When Benign Apps Become Evil. "Once the app passes the review and is installed on an end user's device, it can be instructed to carry out the intended attacks. The key idea is to make the apps remotely exploitable and subsequently introduce malicious control flows by rearranging signed code. Since the new control flows do not exist during the app review process, such apps, namely Jekyll apps, can stay undetected when reviewed and easily obtain Apple’s approval."
Read 4 remaining paragraphs | Comments