Some users of Kim Dotcom's Mega storage system are in a lather about a new browser extension that extracts their master encryption key from computer memory and displays it in a window. While the recently unveiled MEGApwn bookmarklet works as advertised, the general weakness it highlights is common across a variety of similar services, including Apple's iCloud. As such, the uproar in response to the hyperbolically named MEGApwn is largely an overreaction.
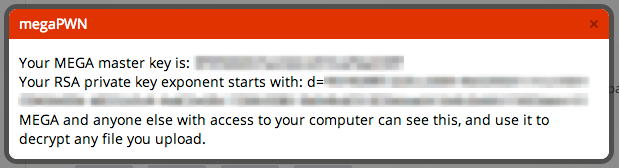
More about that in a moment. First, a quick description of the software itself. MEGApwn is a bookmarklet containing JavaScript commands that extend a browser's capabilities. When imported into a compatible browser, it plucks any Mega master encryption keys that may be stored in memory and displays them to the user. The takeaway according to creator Michael Koziarski: it's not as hard as many people think for a criminal hacker or a government agency armed with a secret or not-so-secret demand to gain complete access to the plaintext files stored in the cloud service.
"Any warrant or subpoena issued to Mega for your files simply has to ask for your master key, which Mega can retrieve, and prohibit Mega from telling you about it," Koziarski's webpage warned. He went on to cite a case from 2007 in which encrypted e-mail provider Hushmail turned over 12-CDs-worth of e-mails from three account users named in a Canadian court order that targeted illegal steroids distribution. According to Wired, the evidence was most likely decrypted by exploiting a vulnerability that allowed operators to log the users' plain-text password when they accessed the service.
Read 8 remaining paragraphs | Comments




