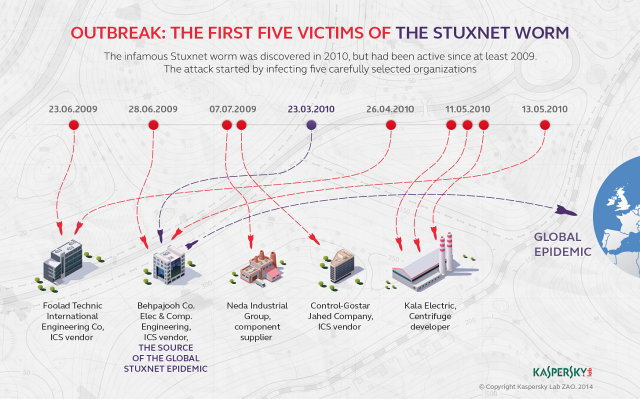
The Stuxnet computer worm that attacked Iran's nuclear development program was first seeded to a handful of carefully selected targets before finally taking hold in uranium enrichment facilities, according to a book published Tuesday.
The new account, included in Countdown to Zero Day: Stuxnet and the Launch of the World's First Digital Weapon by Wired reporter Kim Zetter, is at odds with the now-popular narrative that the malware first penetrated Iran's Natanz enrichment facility and later unexpectedly broke loose to infect hundreds of thousands of other sites across the globe. That earlier account, provided by New York Times journalist David Sanger, characterized the escape outside of Natanz as a programming error that was never intended by engineers in the US and Israel, the two countries Sanger and Zetter said devised and unleashed Stuxnet. According to Zetter, the world's first known cyber weapon first infected Iranian companies with close ties to Iranian nuclear facilities and only later found its way to Natanz.
"To get their weapon into the plant, the attackers launched an offensive against four companies," Zetter wrote. "All of the companies were involved in industrial control processing of some sort, either manufacturing products or assembling components or installing industrial control systems. They were likely chosen because they had some connection to Natanz as contractors and provided a gateway through which to pass Stuxnet to Natanz through infected employees."
Read 6 remaining paragraphs | Comments