Enlarge (credit: Randomizer.com)
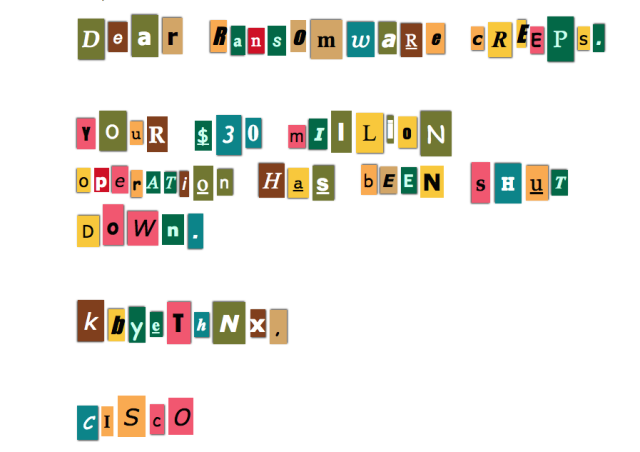
Security researchers have disrupted an online criminal operation they estimated drew $30 million per year pushing ransomware on unsuspecting people browsing the Internet.
The takedown was performed by investigators from Cisco Systems' Talos security unit, which was researching the Angler Exploit kit. The hack-by-numbers tool is sold in underground crime forums to people who don't want to go through the hassle of developing and testing exploits themselves. Angler is one of the most potent of the exploit kits available, with the ability to successfully infect an estimated 40 percent of the end users it targets using attack code that surreptitiously exploits vulnerabilities in browsers and browser plugins. In most cases, the security flaws have already been patched, but, in some cases, the kits exploit zero-day vulnerabilities for which there is no currently available fix.
The Talos researchers quickly noticed that a large percentage of infected end users were connecting to servers operated by service provider Limestone Networks. After getting the cooperation of Limestone and examining some of the servers responsible for carrying out the operation, the researchers found that the single operation was targeting as many as 90,000 end users per day. They estimated that if just three percent of targets paid the average ransom demand of $300, the operation would generate more than $30 million in 12 months. The estimate is consistent with log files retrieved from just one of the servers accessed by Talos researchers. It showed the operation generating more than $3 million.