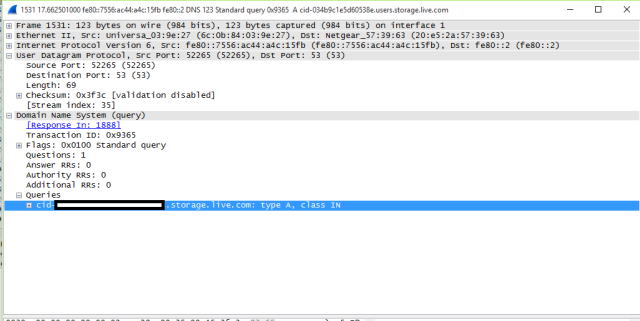
The blocked text is Ars IT Editor Sean Gallagher's Microsoft user account CID, exposed in a DNS lookup. The same data was exposed in a TLS server name indicator field in plaintext. (credit: Sean Gallagher)
If you think using secure HTTP would be enough to protect your privacy when checking webmail, think again. When users connect to their Microsoft user account page, Outlook.com, or OneDrive.com even when using HTTPS, the connection leaks a unique identifier that can be used to retrieve their name and profile photo in plaintext.
A unique identifier called a CID is exposed because it's sent as part of a Domain Name Service lookup for the address of the storage server containing profile data and as part of the initiation of an encrypted connection. As a result, it could be used to track users when they connect to services from both computers and mobile devices, possibly even identifying users as their requests leave the Tor anonymizing network.
In a lab test, Ars confirmed the leak, first publicized this weekend by a blogger based in Beijing. Packet captures of connections to Outlook.com, the Windows account page, and OneDrive.com revealed DNS lookup requests for a host with the format cid-[user's CID here].users.storage.live.com. The CID is also embedded in the Server Name Indication (SNI) extension data exchanged during the Transport Layer Security "handshake" that secures the session to the services, as Ars confirmed in an inspection of the packets.