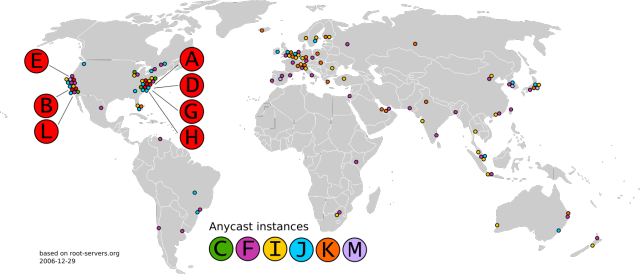
Enlarge (credit: rootservers.org)
Early last week, one of the most vital organs of the Internet anatomy came under an unusual attack. On two separate occasions lasting an hour or more each, a flood of as many as many as five million queries per second hit multiple domain name system root servers that act as the final and authoritative reference for determining which IP address is returned when a user types a domain name into a browser.
The first barrage took place on Monday, November 30, and lasted for about two hours and 40 minutes. The second one happened a day later and lasted for almost exactly an hour. Most but not all of the 13 root servers that form the Internet's DNS root zone were hit. The attacks started and stopped on their own and consisted of billions of valid queries for just two undisclosed domain names, one for each incident. There's no indication of who or what was behind the attack.
While the load was large enough to be detected on external systems that monitor the Internet's root servers, they ultimately had little effect on the billions of Internet end users who rely on them. That's partly because root servers provide IP translations only when a much larger network of intermediate DNS servers fail to do so and partly because of the robust design of the hundreds of servers that run the dozen-plus root authorities.