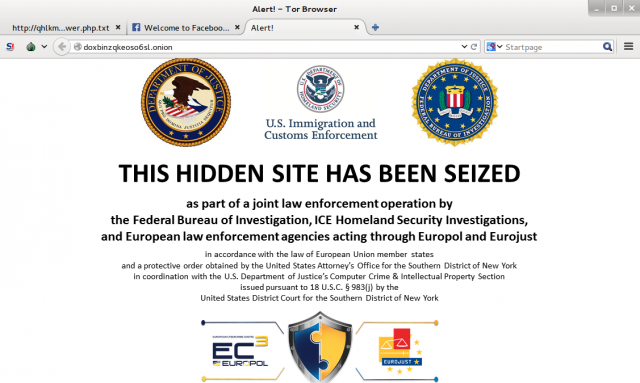
In a blog post written on November 9, Tor Project director Andrew Lewman went over the possible ways that over 400 hidden services on dozens of servers were located by law enforcement during Operation Onymous. While some of the servers were related to criminal activity (such as Silk Road 2.0), at least some of the servers were not—including several that were acting as infrastructure for Tor’s anonymizing network. And the only answer Lewman could currently offer as to how the sites were exposed was “We don’t know.”
That's unnerving not just to people like the operators of the many illicit sites that were taken down by Operation Onymous, it’s also of concern to anyone using Tor to evade surveillance by more oppressive governments. Activists, dissidents, and journalists, for example, all rely on the same Tor infrastructure.
“If you are an activist or a journalist in these countries, your government thinks you are a criminal,” Eva Galperin, Global Policy Analyst for the Electronic Frontier Foundation, told Ars. “And you can learn a lot about good operational security practices by watching where criminals go wrong reading the affidavits on these cases, because your government is treating you as a criminal.”
Read 16 remaining paragraphs | Comments